Forum menu
Decent summary in accessible terms.
No Internet, No Email,
OT but yesterday external router down and email servers are off-site so no internet and no email.
did I send out an email to everyone telling them email was down then realised what I'd said just as I hit send?
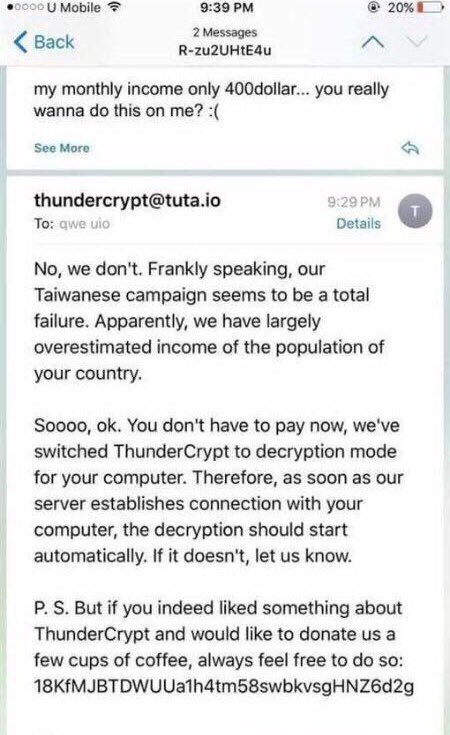
The guys who wrote this ransomware offer customer support.
For clarity, "this ransomware" is the malware in the post, it's unrelated to (but similar to) WannaCrypt.
In related news, I'm now working on servers that cannot be patched, disabling SMBv1. Yay.
Did we ever discuss that it appears the vast majority of computers affected were running W7 (I've seen suggestions of 99%)? So it wasn't really a problem with stopping support for XP, but with not applying available patches to 7
I mentioned it a couple of times.
http://singletrackworld.com/forum/topic/nhs-in-large-scale-it-shutdown/page/3#post-8469449
http://singletrackworld.com/forum/topic/nhs-in-large-scale-it-shutdown/page/7#post-8472827
It's almost certainly a primarily Windows 7 issue.
The best figures I have for the NHS is that XP accounts for about 5% of their workstation estate.
Interesting, missed that before
My win 7 machine refuses to install windows updates and just throws a hissy fit installing to 99% then uninstalling then installing again locking the machine up for a day so I'm relying on the fact that -
a) I don't store anything on it that I'm not willing to lose
b) I don't click on anything dodgy.
Have you added an internal DNS reg and a sinkhole server Cougar? Seems an easy way to stop the next variant firing, just by following twitter.. might even be scriptable / bott-able.
We did this first thing, SMB v1 was already off by policy on 99% of the clients, apart from GxP stuff (that's pretty well hidden anyway) for performance issues. We're near 100% W7 client wise.
My win 7 machine refuses to install windows updates
Google "windows update fixit"
Have you added an internal DNS reg and a sinkhole server Cougar?
Internal DNS is out of my hands these days. In any case, any new variant will almost certainly use a different killswitch (or not use one at all).
[quote=jambalaya ]Interesting, missed that before
Well to some extent it was just rumour at the time - there's now decent info on what actually was impacted. There has also been some dodgy use of statistics - apparently 90% of NHS trusts have some machines running XP and I've seen that figure totally misinterpreted by people who should know better.
I think if I had a W7 machine which wouldn't install updates I'd be doing a clean install - it's not just this vulnerability but other future ones (if it's on a network, it's not just the data on it you need to worry about).
^^ thanks. One of my French BILs has a number of XP machines connected to lab kit but none are on the internet. (Asked for help here when one died). Cost of software licence update is uneconomic vs kit which works perfectly well
[quote=jambalaya ]One of my French BILs has a number of XP machines connected to lab kit but none are on the internet.
There's not much risk doing that - provided of course you are also careful about other infection vectors such as USB sticks. There's nothing inherently wrong with XP and I've advised people to do similar (I also had a non connected XP machine here running after support ended, and we had XP running on VMs which were restored from snapshot every restart, though they've now been phased out).
Well to some extent it was just rumour at the time
I had it confirmed pretty quickly, an infosec took it to bits to find out. It was just reported by absolutely no-one, because who listens to experts when there's newspapers to sell.
There's not much risk doing that
"Not connected to the Internet" doesn't necessarily mean "not on a network." With unpatched machines it's perfectly possible for an Internet-connected PC to become infected and then for that to spread to other machines not on the Internet but still networked up.
"Quick! Update the servers and infrastructure so our data is protected."
tech:"But we've done no testing?"
"Just do it!"
*some time later*
tech:"We've done all the updates."
"but no one can login"
tech:"yeah, that's how secure it is!"
"and some of the data's gone"
tech:"errrm, yeah.Still the server's are all patched now which was what you said you wanted."
"why didn't you warn me?"
[i]The computer failure — that Queensland Health Minister Cameron Dick will tell Parliament of today — is most likely as a result of his department’s efforts in fending off “a very serious ransomware attack”.[/i]
[url= http://www.cairnspost.com.au/news/cairns-hospital-suffers-software-catastrophe-with-possible-loss-of-patient-data/news-story/c828de3f4a0f73132ec3d19284cbae88 ]http://www.cairnspost.com.au/news/cairns-hospital-suffers-software-catastrophe-with-possible-loss-of-patient-data/news-story/c828de3f4a0f73132ec3d19284cbae88[/url]
Aye, compatibility testing of hotfixes is a given, but that _should_ have been done in the two months between the patches being released and the malware's first hit.
People just do not like to patch if they know it is going to harm productivity.
The thing is most IT departments aren't staffed to cope with the bursty nature of proper patch testing. Where I work we deploy to a few test environment PCs but they only run some of the core apps (we can't afford to run every single prod app in the test environment, as I doubt many businesses can). Once the basic testing has been done it's pushed into live to a select set of PCs, if no issues are reported it's pushed to the remaining several thousand PCs, there's only time to do this quarterly and allow for a sufficient amount of testing (along with all the other work going on). Even then it's impossible to test everything (hundreds of apps and some functions are only run monthly or annually).
I'm not making excuses for the IT departments out there that still can't be bothered to patch routinely but the general perception from the public of this being the case with anyone that suffers an outbreak from malware where a patch already exists isn't correct.
.