Looks like they've taken the decision to shut down a large part of the NHS IT infrastructure to protect it from attack.
[url= https://www.theguardian.com/society/2017/may/12/hospitals-across-england-hit-by-large-scale-cyber-attack ]https://www.theguardian.com/society/2017/may/12/hospitals-across-england-hit-by-large-scale-cyber-attack[/url]
Try not to get sick for a few hours people 🙁
beggars belief sometimes... what are the hackers trying to prove. !?^"%£^**
tuskaloosa - Member
beggars belief sometimes... what are the hackers trying to prove. !?^"%£^**
Nothing, it's just the usual ransomware by the sound of it. Bloody annoying but it is fairly indiscriminate when it comes to targets. Some of it is very advanced in terms of avoiding detection as well.
I hear from (cough) facebook GP groups (/cough) that some GP software servers are down too.
Not mine however. Singletrackworld and the Poke are what leads to naff productivity at my end...
DrP
Yep all our systems have gone down
Just hope contingency allows clinical things to keep going. Major incident plans in action
Attack a bank etc is one thing, this could affect people's lives 🙁
bits of Blackpool and Blackburn effected AFAIK
Should have used Linux.
Ugh. I work in the IT dept of a local authority.
We had exactly the same last year. It was a massive pain in the arse, ended up using a similar strategy to that which it looks like they're using. Minimise attack surface, repair, slowly bring stuff back up in conjunction with AV supplier. Painful enough for a small authority, going to be hideous for the NHS 🙁
The attackers probably aren't targeting the NHS specifically, there'll just be a script that goes around probing ports and then seeing if it can install the ransomware. The other possibility is that it was on a memory stick and only became activated if it found it was on a large network or similar trigger.
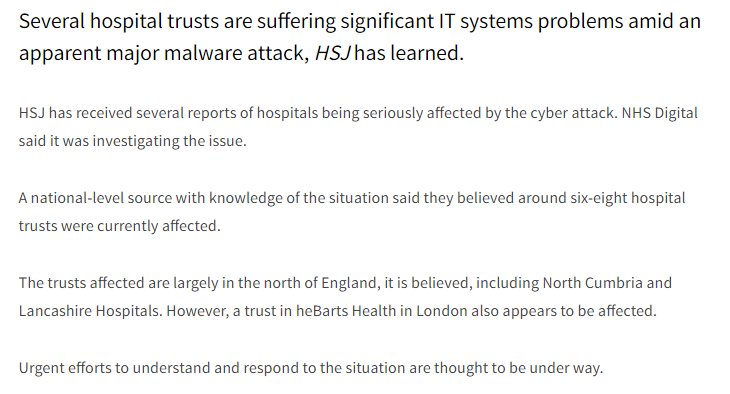
BBC reporting:
[i]GPs are resorting to using pen and paper[/i]
read into that what you want.
GPs are resorting to using pen and paper
'Uh Oh! Your files have been encrypted. By indecipherable handwriting!
The other possibility is that it was on a memory stick and only became activated if it found it was on a large network or similar trigger.
The non joined-up nature of NHS IT is our greatest defence. 🙂
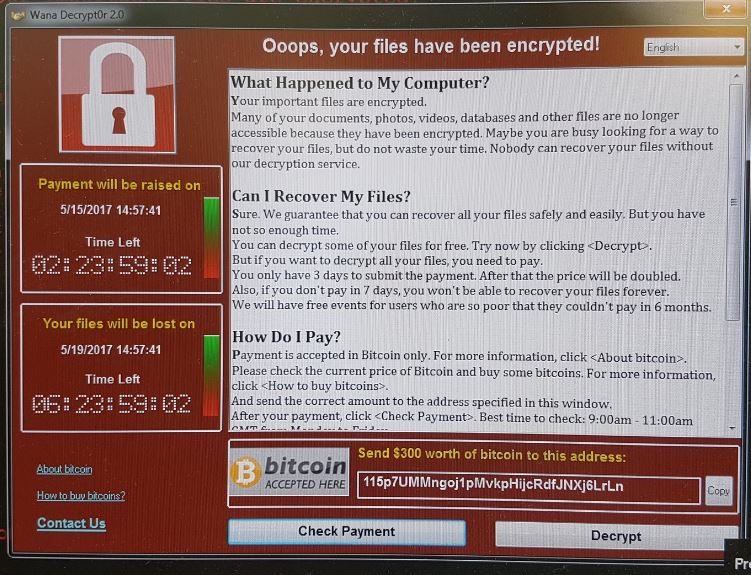
Kind of the hackers to offer payment terms for the poor!
The attackers probably aren't targeting the NHS specifically, there'll just be a script that goes around probing ports and then seeing if it can install the ransomware. The other possibility is that it was on a memory stick and only became activated if it found it was on a large network or similar trigger.
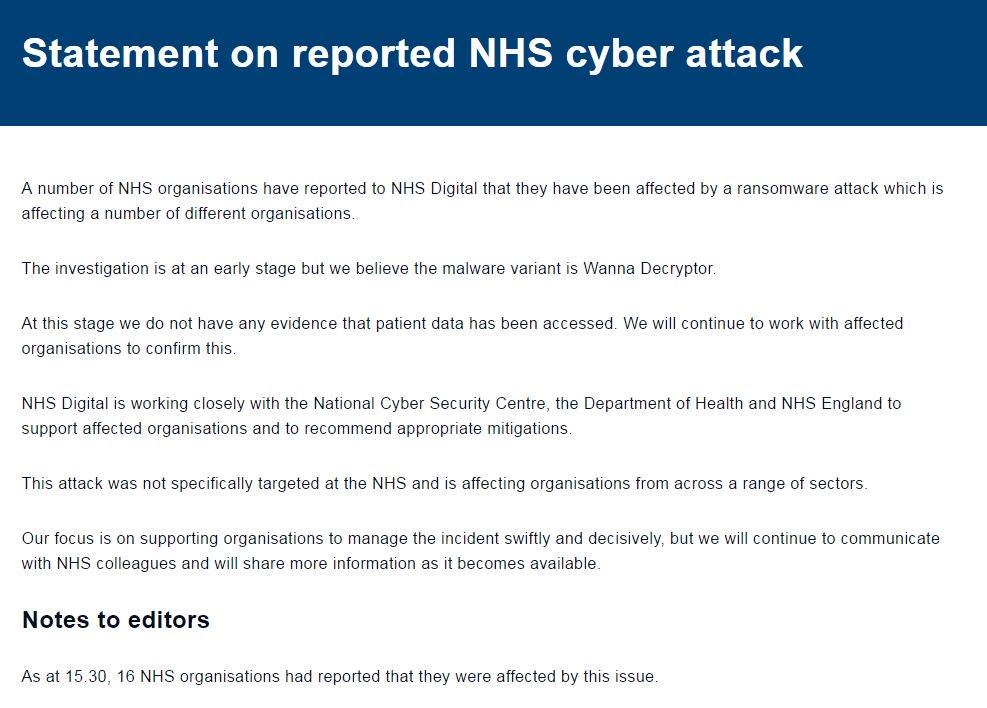
As you say, I'd be very, very surprised if it was targeted. It's 'just' run of the mill, indiscriminate malware 🙁
I know if one that came in via email, was blocked, and then subsequently released, upon which the recipient opened it. At which point it identified attack surface, which are usually open file shares on servers, hops on to them, and propagates from there.
I await the Russian conspiracy theorists though. (And to be fair it's almost certainly of Russian origin)
There was a really interesting RadioLab about this last year as well.
#nhsspendingonITendsinfailureshocker
Re: memory sticks. Read up on [url= https://www.wired.com/2014/11/countdown-to-zero-day-stuxnet/ ]Stuxnet[/url] which was the virus that attempted to destroy Iran's nuclear fuel enrichment program. Really, really targeted: it would only deploy if it found a particular version of certain firmware in a certain configuration. Basically they knew exactly what they were after. The above link is quite a long article but well worth reading.
We have also been targeted today by ransomware affected emails, not NHS, so this could be part of a much larger ransomware attack.
Affecting our local Dgh. No reporting on CT/xray/bloods. Handwritten triage and wristbands. It's distinctly possible that real patient harm will come from this attack due to the delays in diagnosis and treatment.
BBC reporting:[b]GPs are resorting to using pen and paper[/b]
read into that what you want.
...then sent on to Bletchley Park to be decoded! 😀
[i]#nhsspendingonITendsinfailureshocker[/i]
although for the most part they'll just be using commercial software the same as everyone else.
The issue with the NHS is that there's so much linked infrastructure that malware can propogate itself very quickly across a large number of sites.
It'll probably end up beign someone who brought a memory stick from home or went to dropbox to pick a file up.
Fixed.It'll probably end up being [strike]someone[/strike] a domain admin who brought a memory stick from home or went to dropbox to pick a file up.
Telefonica telling employees to disconnect 'puters from networks.
[url= https://teiss.co.uk/2017/05/12/telefonica-ransomware-attack-employees-asked-pull-plug-computers/ ]https://teiss.co.uk/2017/05/12/telefonica-ransomware-attack-employees-asked-pull-plug-computers/[/url]
The worst thing about all of this is that the banks could if they wished trace the route of the money.. but banking secrecy wins.
GP software servers
Is that some sort of slave labour that GPs can afford on their £1,000,000 p.a. salaries?
Does anybody actually pay to this sort of demand?
Yes.. in my experience.. lots do pay.
Does anybody actually pay to this sort of demand?
People with valuable data and no backups. It's the only way to get the data back. Think of it as an idiot tax.
The worst thing about all of this is that the banks could if they wished trace the route of the money.. but banking secrecy wins.
Bitcoins?
Yes. Everyone from private businesses to local authorities to private individuals have paid.
Is be very surprised if the money could be traced, as the ransom demand will almost certainly be payable only via bitcoin.
Edit: beaten to it!
I don't know much about cyber security, but presumably this software is constantly prowling the net looking for vulnerable ports or whatever, so you'd expect the problem to be much more widespread unless they were slack with thier firewalls etc?
I suppose it's more likely a user with too many account privelidges unwittingly caused it?
Think of it as an idiot tax.
Dressed like that they were asking for it
mattyfez - Member
I don't know much about cyber security, but presumably this software is constantly prowling the net looking for vulnerable ports or whatever, so you'd expect the problem to be much more widespread unless they were slack with thier firewalls etc?I suppose it's more likely a user with too many account privelidges unwittingly caused it?
It is very widespread, there are a huge number of variants and there are new ones released constantly targeting new exploits.
I have seen the devastation ransomwhere caused at a biotech company, it was not pretty. And they were pretty shit hot on computer security. Unfortunately they also found out that day that some of their backups had been silently failing.
Strong and Stable eh?
May got a pasting from NHS staff calling in on LBC this morning too, she's lucky it wasn't after this...
I think most ransomware comes from emails, not from hacking attacks. Humans are the weakest link in the security chain.
I know of two companies affected by this.
1 reverted back to previous nights backup. Lost half a days work.
The other paid up and got a decryption key. It worked.
In one of the instances the culprit was a macro enabled word document e-mailed in. Downloaded and executed code from the internet on opening. It then encrypted every file on any share that was connected.
I feel for the NHS on this one. Going to be very painful to recover...
You make it sound so sinister.this software is constantly prowling the net
MSP is correct. It (or they rather) just relies on the easiest attack vector. Dopey humans and their inbox. Someone runs the program they have been sent (cutest_kitten_EVER.jpg), and then it runs in the background encrypting any drives on your computer. Which in this case looks like someone with a high level of access to write to network shares.
.
Why aren't email clients sandboxed?
An email client needs to be able to [i]read[/i] files, and create [i]new[/i] files, but not [i]modify[/i] existing files. Along with any child processes.
Dressed like that they were asking for it
I didn't say they deserved it. Rather it's an eggs-and-baskets disaster waiting to happen.
Because it's not the email client executing the program. It's the user.
Which is why ransomware like this is hard to stop. People (and computers if we want to get technical) need to read, write and execute files to do their job.
Because it's not the email client executing the program. It's the user.
Quite. Sandbox emails - then what happens when a user gets an emailed spreadsheet, opens it, edits it and wants to save it to their Documents folder?
Which is why ransomware like this is hard to stop.
It's trivial to stop. Remove "execute" privileges from temp directories. You can do it organisation-wide via Group Policy in a few mouse clicks. (Ok, users can bypass this by saving the attachments elsewhere, but it'll stop most if not all double-click-oh-shit infections.)
Also effective but slightly more difficult: Remove rights to run unsigned code, and / or whitelist allowed apps for regular users.
I think this may be using a SMB vulnerability rather than just a standard easily stopped executable.
Meh - they have business continuity procedures, don’t they? Just use them. That’s what they are for.
Oh, they don’t you say? Well, somebody’s head should be on the block after this, then...
edit - for context, I used to work for a Pharma company, supplying the NHS. We were *required* to have business continuity procedures, and test them, before the NHS would even deal with us.
Rachel
It's still got to get in in the first place though.