Aye. If you refuse to give a specimen at the roadside you can also be charged with drink driving remember.No you can't. You can be done for 'Failing to provide a specimen for analysis', however.
If you're over the limit and driving then you're posing an imminent danger to the public. Similarly the police have the right to search a house without a warrant if they suspect a child is in imminent danger (at least that's what they told me when they were looking for a child belonging to a past occupant).
OTOH requiring someone to hand over their encryption keys is only of use for gathering evidence after a suspected crime (or as part of a fishing expedition). Searching a building with a warrant is a passive process- it doesn't require you to actively do anything.
Once he's released, does he get his computer back?
It's not a legal question, it's a bureaucratic one. In practice you rarely get anything back from the police.
...rather than your fanciful account [any evidence of this being true here?]
I did actually provide a link but let me help you out a bit:
http://lmgtfy.com/?q=GaryMcKinnon
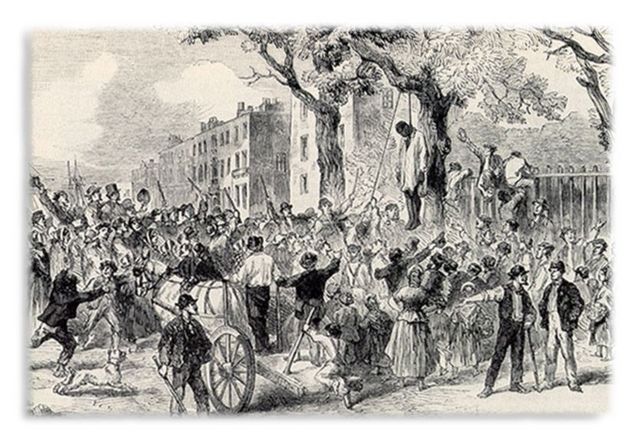
just to add, if I was involved in something like the McKinnon case I would defiantly not give up my password and take the prison sentence, and the risk of being strung up by an angry mob.
Aye. If you refuse to give a specimen at the roadside you can also be charged with drink driving remember.No you can't. You can be done for 'Failing to provide a specimen for analysis', however.
If you're over the limit and driving then you're posing an imminent danger to the public.
But you can be charged with failing to provide a specimen and banned from driving as a consequence even where you haven't touched a drop. And in some circumstances where you haven't been driving either.
TandemJeremy - Member
No - its nothing to do with his right of silence - its about allowing police to search his computer without obstruction - same as he cannot stop them from entering his house when they have a valid search warrantVirtual or physical search - its still a search
Okay, so back to what I asked earlier. If you have a physical safe in your home and your house is searched by the Police, can you be forced to reveal the code?
rather than your fanciful account [any evidence of this being true here?]
you really missed my point here. Have you any evidence that this [ufo searching ]is the reason this person [ie here - the case we are talking about ]did not give over their password? I am aware that the case you mention is real but ,as I mentioned in my post, have you any evidence that this is the reason this person - traced via child pron links- refused to give up their password? No hence why I said it was a fanciful account of this case.
Not sure if what I wrote is unclear or you just took it the wrong way tbh.
if I was involved in something like the McKinnon case I would defiantly not give up my password and take the prison sentence, and the risk of being strung up by an angry mob.
We know if someone is guilty of an offence and they dont like the sentencing they will avoid giving over the password/evidence to sentence them whether it is hacking or child porn. Yes criminals try to avoid capture... the issue is what we do when someoen doe shtis over a computer password
If you were innocent and accused of either would you give up your password?
Shall we not just stick to this case. As I said in my original post [ which you could have taken as a clue i had heard of him] I would support mc Kinnon - not because he is innocent but because the extradition treaty is one sided and the potential sentence too harsh for me to consider it justice if we extradite him.
Fair enough, sorry thought you were saying [i]I[/i] made the whole McKinnon case up.
Anyway, I guess I'm not saying that under current law he shouldn't have been sent to jail since RIPA clearly gives the authorities the power to lock him up.
If I was innocent of everything (although I think that the chances of anyone not having any evidence of anything illegal on their computer is low) and accused I really don't know what I'd do. On the one hand I'd want to take a stand and challenge the law as an infringement of European privacy laws. On the other hand, if I had been publicly branded as someone hiding images of child pornography, basically a paedophile, and was being sent to prison where I don't think people take kindly to nonces then it would be a difficult decision.
I think that RIPA is a horrendous piece of legislation. It should be fought at every opportunity but is it worth it if the authorities are going to brand you as a paedophile for non-compliance?
Okay, so back to what I asked earlier. If you have a physical safe in your home and your house is searched by the Police, can you be forced to reveal the code?
I don't know is the answer - but I would be fairly sure the cops would be able to open it without the code and without damaging the contents
In practice you rarely get anything back from the police.
🙄
That wasn't what I was asking. Police would be obliged to return property to a person at the conclusion of an investigation/case.
Does anyone actually know if he could get his computer back afterwards? Or would the police keep it for further investigations? Would they have the legal right to do so? Or would they be obliged to return it, if they can't break the password?
TandemJeremy - Member
I don't know is the answer...
Bloody hell. I'm going to frame that!
Blimey TJ; feeling ok? 😯
If he asks for his computer back the police should ask him to say the magic password.
He wasn't black though, there's a photo in the article.
Quite interesting, its been threatened for a while and I had a couple of cases a long time ago where they eventually caved and provided the keys or password. One was irrelevant as we'd borken into it but the other was churning away for 2 weeks and was getting there albeit slowly. Thats the problem, its a function of time/power to crack 50char passwords, even with known keyspace searches it could be cracked on pass 1 or pass 50^n.
Whoever it was that asked about proving usage vs virus - its quite obvious once you start to look at the data. Private modes in browsers make this all a bit harder now but essentially there is still a lot of cached information which you can/could use to recreate sessions, map patterns and the like.
And there are drives that spin 2 ways - one way has an unencrypted volume on it, the other way has a fully encrypted volume. You need a key (smartcard) to set it spinning the right way.
I used to run a computer forensics company and wrote disk imaging software so i've got a little bit of background in this 😉
My home computer is encrypted with a 65 letter pass sentence. I don't do anything dodgy, I just don't want a theif to steal my computer and get access to all my files/banking details. Having said that, I have forgotten the sentence once and had to wipe the system and start from scratch, which is annoying, despite using it daily.
Yes, but if the police knocked on your door, would you refuse to give them the password and go to prison?
No, but if I said I forgot it (as i probably would if I were a dodgy person hiding stuff) what the hell can they do? They can't jail you for ACTUALLY forgetting your password surely, even if that risks missing some people who fake forgetting it? And in order for it to be a deterrant, they'd have to make the term equal to the term for the crime suspected, and there's no way that'd fly.
"Once he's released, does he get his computer back?" no they ask him again he refuses again. That refusal is a fresh and separate crime so back in the same position.
The computer will be retained until accessed if it contains evidence that has been used in crime it can be destroyed at the end of any successful prosecution.
If it has any child porn images on it's hard drive even if he is innocent then it will be destroyed it would be an offense for the police to return it to him.
"Once he's released, does he get his computer back?" no they ask him again he refuses again. That refusal is a fresh and separate crime so back in the same position.
So if you really do forget your password you're in big trouble - that would appear to have a life sentence with no parole.
I'd best give my pass-phrase to the local plod for safe keeping!
I'm not letting you in to my house cos someone may have buried a murdered body under the living room etc.
While I appreciate the possibility of viruses using a third persons PC as an illegal server I would have thought that other evidence would come to light to support ones innocence. Would you even be being investigated in the first place if your weren't actually carrying on in other ways that would point to your guilt in the crime you were accused of?
As for commenting on legality, I am in no form an officer of the law so my comments are speculative. I suspect the "anything that you say may be used as evidence against you/ that you do no say may not be used in your defence" is in a totally different area than search warrants and searching for evidence.
And isn't it good that so many people were bullied at school so that they would feel harassed enough in later life to become Police officers. Could the country would be in great shape with no law enforcement. I'm not suggesting the system is perfect, nothing ever is.
Here endeth the sermon
Been saying for years that a "proper" wrong-un would take the prison for not revealing encryption keys over having the police find out what they'd been up to. That said, nearly all the RIPA requests I've seen have been relatively reasonable, following up reports of illegal activity. Amazing though, how many police forces call up and just expect you to hand over the info without a court order or a RIPA request.
I've met the guys who do the forensics on these cases, and they were very convincing. They typically go in after they get server logs, credit card details etc from kiddy porn websites that get shut down. Essentially they have to have very strong suspicions before going in, because a forensic investigation is an awful lot of work and there aren't many people who do them in the uk.
The was it a virus vs deliberately downloaded thing, they are pretty good at that - apparently it is quite easy to tell the difference, and to collect evidence for it. It's also the case that people they bother prosecuting will typically have tens of thousands of images, which even the most lax about security people would probably notice a virus downloading.
He should have used TrueCrypt's 'duress' system
I understand that in at least one case, they have actually detected the inner volume of a truecrypt at which point they asked for the password again. Some clever mathematical proof that I think was quite cutting edge - whilst a lot of what they do is pretty mundane, they have a few bloody clever guys working for them.
They can't break something like this password though I think - even with only letters, it'd have 26^50 combinations -, and dictionary attacks wouldn't work on a multi word password either.
Joe (insomniac nerd)
Whoever it was that asked about proving usage vs virus - its quite obvious once you start to look at the data. Private modes in browsers make this all a bit harder now but essentially there is still a lot of cached information which you can/could use to recreate sessions, map patterns and the like.
See. Browser history, like I said before! 🙂
After I heard those anti-terrorist hotline adverts I was extremely paranoid and very worried about my privacy.
Question for legal people. If you get reported by your friend or neighbour, how much surveillance can you be put under? Can they check with your ISP to see what you're doing online?
If you seem to be to be taking steps to hide your online activity with things like Tor, proxy servers, VPN and that kind of thing would that be considered evidence of wrongdoing and could it result in a warrant to search your computer?
I've tried to decipher RIPA but it all seems very vaguely worded when it comes to what evidence of wrongdoing is.
Anti-terror adverts i was thinking about