I should have added 3 years to suss out infection via USB FFS! but for once I was trying to be a bit diplomatic and limited it to some of it seems plausible.
Couple of demos from the ErrataSec guy:
[b]Robert David Graham ?@ErrataRob
[/b]
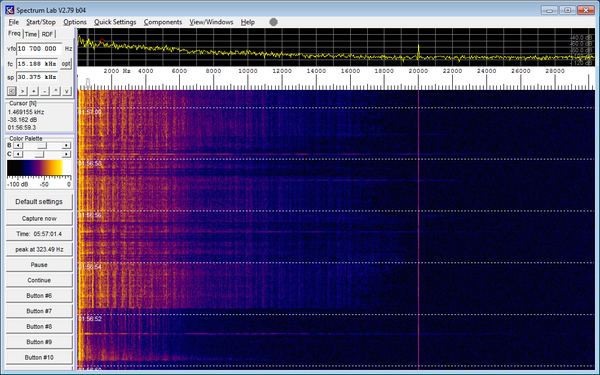
Left notebook receives 20khz carrier generated by notebook on right while dubstep plays background:
[img]:large[/img]
Closer look, showing 20khz carrier visible. This is NOT #badBIOS, just a simulation showing ultrasonic coms possible
-- from Twitter: https://twitter.com/ErrataRob/status/396157617283686400
Interesting stuff!
Again, no one is arguing about the technicslities of this. Not of the technical stuff sounds particukarky difficult although the communication over audio seems pretty pointless..
That it's been going on for three years and this he's has been investigating for weeks tells you that something is amiss. hes not the only security expert out there but hes the only one who is paying this much attention.
Believe it if you want. I've got tens of thousands of devices to protect and I'll focus on the real threats.
The individual elements sound feasible to me. I say plausible.
virus checkers could be made to validate bios for this. Ultimately, it's just a new vector for a virus.
interesting read. have also watched defcon/blackhat type vids, plus watch hak5 pretty much every week, so all though far fetched, i could certainly believe parts of it.
funnily enough the Hak5 ep i was catching up on just 2 days ago was exactly this... communicating with a laptop that has no wireless or wired network connection, and no USB. one method was audio, but in audible range, and the other was via 2D barcodes and webcam.
It may have had USB, but that is definitely an attack vector too. Especially as every single machine out there independent of OS (Mac, Linux, Windows, Solaris, BSD, ... doesn't matter) has one interface that is automatically always trusted.
[url= http://blog.erratasec.com/2013/10/badbios-features-explained.html ]http://blog.erratasec.com/2013/10/badbios-features-explained.html[/url]
some more on the topic
I'm amazed that in 3 years he hasn't managed to dump the BIOS from one of his "infected" machines and just compare it with what's supposed to be in there, hence I'll keep my cynic hat on for now.
People thought malware designed to corrupt industrial applications was a fantasty - until Stuxnet was discovered.
No, they've been theorising this and in some places taking it quite seriously for years.
There are many ICS infection vectors that were around long before Stuxnet. Stuxnet used not one but three zero day vulnerabilities to propagate, that's how serious hackers with multi-million pound development budgets go about their business. They assign targets, they keep their secrets secret and they attack targets worthy of the investment they have put in.
They don't spend years developing highly advanced attack methods and then pass it over to a small time security researcher.
virus checkers could be made to validate bios for this.
Not so sure. If a virus checker has to make BIOS calls to check the contents of the BIOS then it'd be possible for the virus to hide itself like rootkits do.
I'm amazed that in 3 years he hasn't managed to dump the BIOS from one of his "infected" machines
Possibly the same kind of issue? Dumping the BIOS from software requires issuing BIOS commands which could be intercepted. You'd need to hook up some hardware that could read the BIOS flash directly.
But you're right - 3 years sounds like a suspiciously loooooong time for a security specialist to do something like that!
I think the possibility that it is infecting microcontrollers is more concerning than the BIOS stuff, as they'd be even harder to detect. Though my cynical mind wonders why microcontrollers would shipped without blowing the write fuse on the flash first? How often do they actually do field upgrades to the firmware of USB sticks for instance?
Something else that ocurs to me at this point - webcams. If you leave a room with a few machines in running this sort of exploit then singalling using using video output and webcam input is also possible - even if it's a frame or two of a QR code after 10 minutes of inactivity - hell you if you're monitoring the webcam you can look to see if anyone's in the room and not using the machine.
It's the mesh aspect of this I don't like.
As samuri says real threats are more important - we don't know what if anything this does apart from reconstruct itself; but I was talking with my "tame hacker" a few weeks ago and we were pondering what would happen if all the firewalls came down. This stuff is a step in that direction.
I'm not saying I'm going to do anything at this point, but I am, shall we say, interested in the fallout from this article.
Yo - samurai - what if he's got it on his machine by accident. You know, Hanlon's Razor?
[i]How often do they actually do field upgrades to the firmware of USB sticks for instance? [/i]
Never would be my guess. I'd be very surprised if USB stick (rather than more advanced USB devices) prom's are even programmable.
Could be wrong of course but it's simply an extension of the USB bus at the end of the day.
[i]Yo - samurai - what if he's got it on his machine by accident. You know, Hanlon's Razor?[/i]
Possible I guess. The coincidence is extreme though.
Dumping the BIOS from software requires issuing BIOS commands which could be intercepted.
BIOS code is mapped into the processor's memory space, you should be able to just dump it with a debugger. Although given the rest of what he's saying maybe this magical malware disables debuggers! But if I was looking at it seriously I'd have ripped out a supposedly infected BIOS chip by now and read it offline.
I'd be very surprised if USB stick (rather than more advanced USB devices) prom's are even programmable.
Could be wrong of course but it's simply an extension of the USB bus at the end of the day.
Yeah me too.
Funnily enough today I'm writing unit tests for a USB driver on a MSP430 microcontroller - but that's for a device that's a bit more complex than just a USB drive.
BIOS code is mapped into the processor's memory space, you should be able to just dump it with a debugger. Although given the rest of what he's saying maybe this magical malware disables debuggers!
Yeah but the action of shadowing the BIOS to main memory requires BIOS commands. Clever malware could supply a clean version or just disable ram shadowing completely since it is usually a user-accessible BIOS option.
But if I was looking at it seriously I'd have ripped out a supposedly infected BIOS chip by now and read it offline.
Yep. Seems like the obvious thing to do if you suspect this kind of thing. Which makes me skeptical, but still interested.
so in all this time he's not shared anything with anyone else on his dodgy USB stick? if this thing is so pervasive why isn't it everywhere already?
maybe it is! 😯
😉
He unplugged the mains, but did he turn off the lights and use a battery powered torch?
Prolly some covert device making the lights flicker, and the webcam is reading the the low-bit rate optical ripple.
edit: and a backdoor in the Intel/AMD chipset to keep the NSA happy
Well we all know how long loading tapes used to take... Freakin ages for a 40kb load.
I call this bollox as the high frequencies would not be picked up by a standard mobo soundcard without you hearing it. If they can get the audio frequencies near the computer I expect they can physically infect it.
[i]after buying a new computer, he noticed that it was almost immediately infected as soon as he plugged one of his USB drives into it.[/i]
Wooo-oooo! It's a ghost!
If they can get the audio frequencies near the computer I expect they can physically infect it.
You seem to be misundertanding the point there. The hypothesis is that the audio-network-thing is for [i]already infected[/i] PCs to communicate without the need for a physical network. I don't think anyone is suggesting it is a primary infection point. That seems to be the USB.
Well we all know how long loading tapes used to take... Freakin ages for a 40kb load.
Not so long ago we were all using 56k modems that used audio to transmit data. You wouldn't want to watch YouTube HD on them - but it is fast enough for small virus payloads.
> How often do they actually do field upgrades to the firmware of USB sticks for instance?Never would be my guess. I'd be very surprised if USB stick (rather than more advanced USB devices) prom's are even programmable.
Well I had a (very careful!) look at that flashboot ru site that the ErrataSec blog linked to and it does [i]look[/i] like you are able to reprogram the controller on a surprising number of flash drives.
(Though I'm not downloading [i]anything[/i] from that site to try it!)
The early mention of booting a MacBook Air from a CD-ROM got my senses a bit tingly and moved the cycnicsm to 11 on the dial.
The early mention of booting a MacBook Air from a CD-ROM got my senses a bit tingly and moved the cycnicsm to 11 on the dial.
This +1.
I'm filing it in the "plausible but bollocks" category.
The early mention of booting a MacBook Air from a CD-ROM got my senses a bit tingly and moved the cycnicsm to 11 on the dial.
http://store.apple.com/uk/product/MD564ZM/A/apple-usb-superdrive
?
[quote=Article] A computer running the Open BSD operating system also began to modify its settings and delete its data without explanation or prompting
Anyone who knows what OpenBSD is might be amused by this...
Whyso?
Anyone who knows what OpenBSD is might be amused by this...
OpenBSD is a standard unix OS, no?
So, all you need to do is start rewriting some text files.
That would be my understanding, I think I just didn't read it as humor. Sorry.
Easy as anything to test the ultrasound theory though, surely? Just need an expensive ultrasound mic connected to a scope. Or, if this isn't total bullcrap, a cheap one pried out of a laptop 🙂
Yeah the most suspicious thing about all of this is how easy it would be to prove or disprove some of these theories, especially for an infosec consultant who specialises in this kind of thing.
And yet we've seen very little in the way of actual evidence.
All very odd.
Still, didn't stop you popping up on Naked Security and putting your oar in did it? 😉
Damn straight!
I was a bit disappointed that a Sophos blog was misreporting it.
Shows they haven't really looked at it properly.
I like the approach of the chap in the original article. Just keep plugging shit in. Whatever you do, don't stop and try a methodical approach. It could be the way the journalist writes it, but it's like reading about someone who keeps getting his wedding tackle caught in a mangle and can't figure out why.
I'll just reference Wired's article on Stuxnet again. It never fails to impress me: http://www.wired.com/threatlevel/2011/07/how-digital-detectives-deciphered-stuxnet/all/
Wired's stuxnet article was a good example of technical journalism.
The company I work for deals specifically with the type of kit Stuxnet would have been designed to disrupt. Our engineers were discussing the discovery in quite some detail. 99% of which was way over my head!
Couple of quotes struck me in that Wired article about Stuxnet:
...this time there was no sign that any other researchers were seriously digging into the code.“We were talking about blowing stuff up!” Chien recalled recently, still amazed at what appeared to be a lack of interest. Instead there was what Chien called “silence like crickets.”
...
“There was silence all around us,” Langner later recalled. “Everybody was thinking, This guy is nuts. We always knew that Ralph is an idiot, and now we have the proof for it.”
which pretty much sums up why I'm willing to consider what dragos says even if it sounds pretty far-fetched.
Just watching last weeks BBC Click and Kate Russell was talking about a smartphone app that allows you to transfer files & pics via the speaker&mic in a phone http://chirp.io/
[b]UPDATE:[/b] A couple of interesting developments:
(The) [url= https://www.schneier.com/blog/archives/2013/11/badbios.html ]Bruce Schneier says[/url]:
"When I first read it, I thought it was a hoax. But enough others are taking it seriously that I think it's a real story."
with some interesting comments from his readers.
[url= https://isc.sans.edu/diary/Happy+Halloween%3A+The+Ghost+Really+May+Be+In+The+Machine/16934 ]Internet Storm Center[/url] is remaining on the fence for now but did say this:
let me lay some propositional logic on you:If Dragos is smart, then #badBIOS is a legitimate malware threat.
Dragos is smart.
Therefore, #badBIOS is a legitimate malware threat.
dragos pops up in the comments to discuss a few points too.
Personally I'm still on the [i]"interested, prepared to listen, but healthily skeptical"[/i] bench.
http://store.apple.com/uk/product/MD564ZM/A/apple-usb-superdrive
Graham, I can't find out how much of the base Mac OS you need to boot a machine but the recovery usb sticks I use at work have to be 8GB or larger to boot a Mac. Hence my sceptiscm about the 650MB CDROM boot.
It isn't clear from the article text what exactly they mean by "Ruiu then tried to boot the machine off a CD ROM":
It says:
Three years ago, security consultant Dragos Ruiu was in his lab when he noticed something highly unusual: his MacBook Air, on which he had just installed a fresh copy of OS X, spontaneously updated the firmware that helps it boot. Stranger still, when Ruiu then tried to boot the machine off a CD ROM, it refused. He also found that the machine could delete data and undo configuration changes with no prompting. He didn't know it then, but that odd firmware update would become a high-stakes malware mystery that would consume most of his waking hours.
He may well have just been trying a cd-bootable version of Linux so he could investigate what was going on (pretty standard thing to try if you think the main OS may be infected or corrupt).
As with everything else in the story, the lack of detail is frustrating and unhelpful.
Don't step out of the walled garden m'kay! Penguins and X's obviously don't play nice together 😉
I would be more impressed if someone else had replicated his symptoms. My personal experience is that nearly all software requires a password to install on OSX, Dropbox updates are a notable exception as is one of the old arcane pref panes I used to use in Leopard. Installation of something with an extra "payload" would be my immediate thought.
I'm not saying it couldn't happen but it would seem unlikely given the lack of detail in the reporting.
Seems there are a growing number of professional skeptics too though. Some of whom have had a look at the data he has provided:
http://arstechnica.com/security/2013/11/researcher-skepticism-grows-over-badbios-malware-claims/
My personal experience is that nearly all software requires a password to install on OSX
If he is correct on the infection vector, which is vaguely described as an infected microcontroller in a USB stick - then it could well be operating outside of user space.
i.e. when an OSX system enumerates and negotiates with the controller on a USB device then that [i]could[/i] well be done by a system process with system -level privileges. [i]And if[/i] there is some buffer-overun or other attack possible there then it [i]could[/i] basically do what it wants.
Extraordinary claims require extraordinary proof.