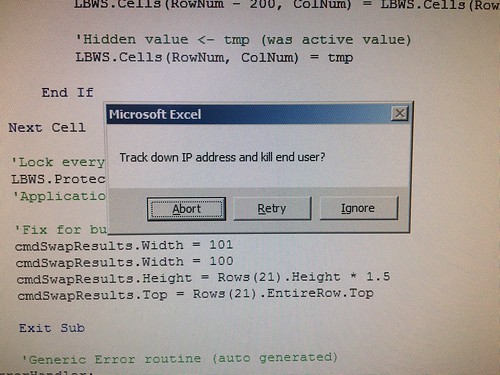
As someone who has to deal with this kind of thing as part of their job trust me when I say it’s probably not worth the effort. With a single IP* you’re on a hiding to nothing…
– RIPE data incomplete/inaccurate
– non-geographic IP assignments
– dynamic IP allocation
– wifi hotspots
– commercial NAT’ing to share connections
– VPNs (and VPN chaining)
– compromised device/server/pc
– reflected or proxied traffic
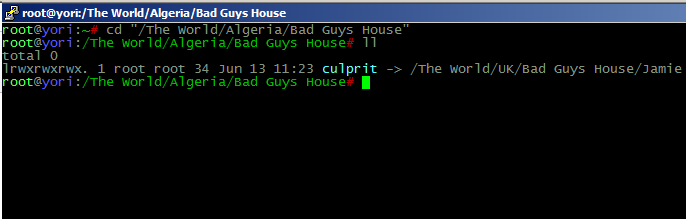
And if none of that is an issue and you get so lucky that its a staitc assignment to the exact person/single device to identify** it as “Joey McAlgerianBlogs in the kitchen with the iPhone” what are you then gonna do? Call the Algerian police and try and make an international incident of it?
If you goal is to perhaps just identify and advise someone that their connection is being used for nefarious purposes then I’ll bet you a KitKat Chunky they’ll fall into one of three camps
1> already know and are sorting it
2> already know and don’t care
3> don’t know and don’t care
* Even if you have loads more you’re basically into circumstantial coincidence level matching, and that’s assuming all data up to date
** and you have co-operation from any/all parties who can match records up, which you probably don’t.